Adopting a Zero Trust Security Model
Move to a Zero Trust Security Model to prevent a data breach
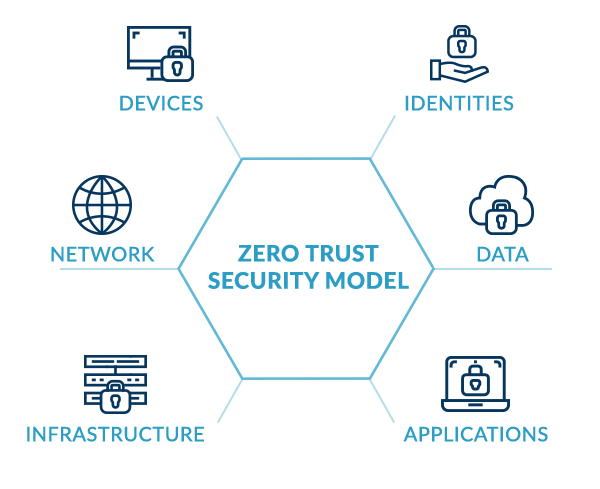
Never Trust, Always Verify
Zero Trust security models operate on the core principle of ‘never trust, always verify.’ The proliferation of cloud applications means that legacy security models with a trusted internal network and an untrusted external network cannot meet the challenges posed by the increasing number of identities and credentials managed by individual users - identity is the new perimeter. A strong Identity and Access Management solution helps organisations build the foundations of a Zero Trust model through centralised access to all applications, whether in the cloud or on-premise, through a Single Sign-On solution linked to the corporate directory.
Benefits of Zero Trust Security Model
Allow users access to only the resources they need, only when they need them
 Protect against the biggest cause of data breaches
Protect against the biggest cause of data breaches
More than 80% of data breaches are caused by stolen, reused or weak passwords. Lay the foundation of zero trust to ensure all applications are protected by secure token-based authentication or Secure Web Authentication, enabling the secure management of the increasing number of cloud identities.
 Deploy maximum protection where it's most needed
Deploy maximum protection where it's most needed
Step-up Authentication enforces that additional factors of authentication are required before accessing more sensitive corporate data and resources, while allowing faster access for routine tasks. Embrace the added security of Multi-Factor Authentication with minimal impact on user experience and productivity.
 Manage access and identity centrally
Manage access and identity centrally
Remove the responsibility of passwords and identities from users and place the organisation back in control. Leverage the existing corporate directory as a single source of truth for identities, and create a Zero Trust architecture to unify access across all cloud and on-premise apps for all users. Ensure only the right users have access to only the right resources at the right time.
 Automate user provisioning and deprovisioning
Automate user provisioning and deprovisioning
Increase efficiency in onboarding new users and providing access to applications with policies that provide just-in-time provisioning linked to the corporate directory. Mitigate the risk caused by users retaining access to corporate applications after leaving their role by automated deprovisioning and revocation of access.
“With My1Login’s IAM solution rolled out within ELEXON, we have put the business back in control of who has access to applications and data, whilst increasing authentication security for all applications. We also now have the ability to quickly provision and deprovision access.”
“We needed a new solution that would work for all of our applications including Windows desktop applications. My1Login’s solution addressed this, as it provided Single Sign-On for 100% of our applications, including Windows desktop apps.”
– Stuart Toner, Senior Information Security Analyst, ELEXON
Read the Elexon Case Study
Products
Ready to get started on your Zero Trust Model journey? Identity & Access Management can be your foundation:

Single Sign-On
Centralise and control user access applications through SSO, ensuring the right people have access to the right corporate applications at the right time. Automatically detect Shadow IT apps and integrate these to ensure access is controlled for all applications within the organisation.

User Provisioning
Automate provisioning and deprovisioning of users to applications to ensure access is strictly controlled. Integrate user provisioning with the existing corporate directory to streamline onboarding and revoke application access when users leave the organisation.

Multi-Factor Authentication
Create a strong Zero Trust model by leveraging Multi-Factor Authentication to protect the most sensitive resources on the network. Utilise step-up authentication to give maximum protection where it’s most required, without compromising user experience or productivity.
Learn More
What is a Zero Trust Module and Why should Your Organisation Adopt it
Read the blog
How My1Login Can Take Your Organisation From Password-based To Passwordless
Read the blog
Why Do Leaders Need to Take The Responsibility of Corporate Passwords Away From Employees?
Read the blog